Securing Connected Pacemakers: A Cyber-Physical Challenge
Published on February 5, 2026 by Admin

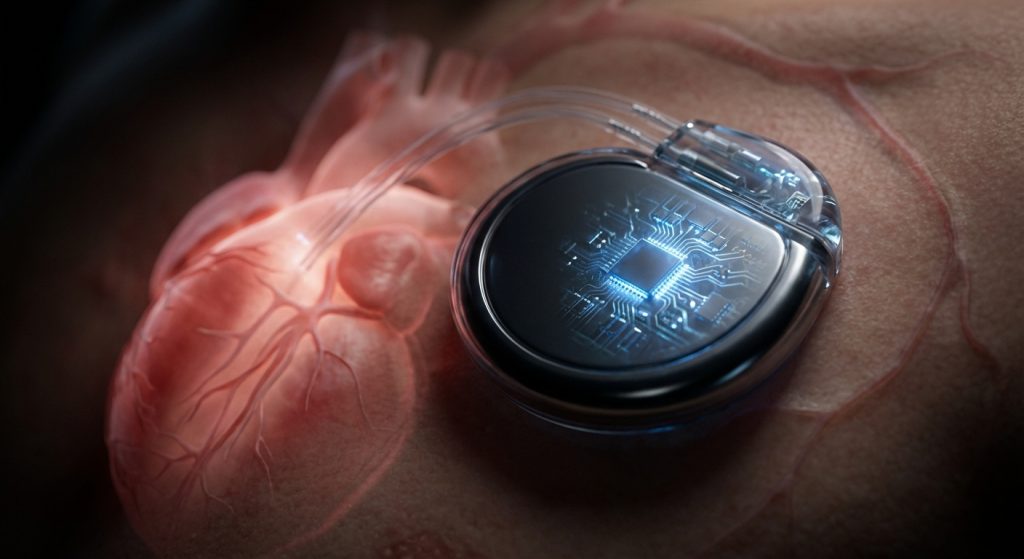
In modern healthcare, technology is a vital lifeline. Connected medical devices offer incredible benefits. For example, pacemakers now transmit data wirelessly. This allows for remote monitoring and adjustments. However, this connectivity also introduces new risks. Cyber-physical security is crucial. This is especially true for devices like pacemakers. Protecting these life-sustaining implants is paramount.
The Rise of Connected Healthcare
Hospitals are increasingly digital environments. Internet of Things (IoT) devices are everywhere. This includes patient monitors and infusion pumps. Connected pacemakers are a prime example. They send patient data to healthcare providers. Doctors can then analyze this information remotely. This leads to better patient care. It also improves efficiency. Furthermore, it allows for faster responses to critical changes.
However, every connected device is a potential entry point. Cybercriminals are always looking for vulnerabilities. They can target any connected system. This poses a significant threat to patient safety. Therefore, understanding and mitigating these risks is essential for IT security experts and medical device engineers alike.
Understanding Cyber-Physical Security
Cyber-physical systems (CPS) combine computation, networking, and physical processes. Medical devices are a prime example of CPS. They interact with the physical world. They also rely on digital networks. Cyber-physical security addresses the unique challenges of these systems. It focuses on protecting both the digital and physical aspects.
For pacemakers, this means securing the device itself. It also means securing the data it transmits. Furthermore, it includes securing the network infrastructure. This holistic approach is vital. It ensures the device functions as intended. It also prevents unauthorized access or manipulation.
The Unique Risks to Pacemakers
Pacemakers are implanted in patients. They directly impact heart function. Any compromise could have immediate and severe consequences. For instance, a hacker could alter pacing settings. This might lead to dangerous heart rhythms. In the worst-case scenario, it could be fatal. Therefore, the stakes are incredibly high.
Moreover, the data transmitted by pacemakers is sensitive. It contains personal health information. Protecting this data from breaches is a legal and ethical obligation. It is also crucial for maintaining patient trust. Without trust, patients may be reluctant to adopt these life-saving technologies.
Vulnerabilities in Connected Pacemakers
Several factors contribute to pacemaker vulnerabilities. Firstly, many devices were not designed with robust security in mind. Early models prioritized functionality over security. As a result, they may have weak authentication or unencrypted communication. This makes them easier targets for attackers.
Secondly, the hospital network itself can be a weak link. Hospitals often have complex networks. They may have legacy systems alongside newer ones. This can create security gaps. Attackers might exploit these gaps to gain access to connected devices. For example, a compromised workstation could be a gateway.
Thirdly, the software and firmware of pacemakers need regular updates. However, updating implanted devices can be challenging. It requires specialized procedures. Therefore, many devices may run on outdated software. This leaves them exposed to known vulnerabilities. Consequently, this is a significant concern for medical device engineers.
Securing the Ecosystem: A Multi-Layered Approach
Protecting connected pacemakers requires a comprehensive strategy. It involves multiple layers of security. This approach is often referred to as defense-in-depth. It means that if one layer fails, others are still in place.
Device-Level Security
At the device level, security starts with design. Medical device engineers must incorporate security from the outset. This includes:
- Strong Authentication: Ensuring only authorized personnel and devices can connect.
- Data Encryption: Protecting transmitted data from eavesdropping.
- Secure Boot Processes: Verifying the integrity of the device’s software.
- Regular Firmware Updates: Implementing a secure and efficient update mechanism.
Furthermore, manufacturers should conduct rigorous security testing. This helps identify and fix vulnerabilities before deployment. It is also important to consider the entire lifecycle of the device. This includes secure disposal.
Network Security Measures
Hospitals must also strengthen their network security. This involves several key areas:
- Network Segmentation: Isolating medical devices from general hospital networks. This limits the potential spread of an attack.
- Intrusion Detection and Prevention Systems (IDPS): Monitoring network traffic for suspicious activity.
- Access Controls: Implementing strict policies for who can access medical devices and data.
- Regular Audits: Periodically reviewing network logs and security configurations.
Additionally, robust firewall configurations are essential. These act as barriers between different network segments. They control the flow of data.
Data Security and Privacy
Protecting patient data is non-negotiable. This involves:
- Data Minimization: Collecting only the necessary data.
- Anonymization and Pseudonymization: Removing or obscuring personally identifiable information where possible.
- Secure Storage: Ensuring data is stored in encrypted and access-controlled environments.
- Compliance with Regulations: Adhering to data privacy laws like HIPAA and GDPR.
The ethical implications of data breaches are significant. Therefore, maintaining patient privacy is a top priority.
The Role of IT Security Experts
IT security experts play a critical role. They are responsible for implementing and managing security measures. They must understand the unique environment of a hospital. This includes balancing security with the need for uninterrupted patient care. They also need to stay updated on the latest cyber threats.
Their tasks include vulnerability assessments, penetration testing, and incident response planning. Moreover, they must educate hospital staff on cybersecurity best practices. This human element is often the weakest link. Therefore, training is crucial.
The Responsibilities of Medical Device Engineers
Medical device engineers are at the forefront of innovation. However, they also bear a significant responsibility for security. They must design devices with security as a core feature, not an afterthought. This requires a shift in mindset. It means considering potential threats throughout the design and development process.
Engineers also need to develop secure update mechanisms. This ensures devices can be patched effectively. Furthermore, they must collaborate closely with cybersecurity professionals. This ensures a unified approach to device security. The field of nanotechnology in drug delivery, for example, also highlights the need for robust security in advanced medical solutions.
Regulatory Landscape and Future Trends
Regulatory bodies are increasingly focusing on medical device security. Agencies like the FDA in the US are issuing guidelines. These aim to improve the security of connected medical devices. Compliance with these regulations is mandatory for manufacturers.
Future trends include the use of AI for threat detection. AI can analyze vast amounts of data. It can identify anomalies much faster than humans. Furthermore, blockchain technology may offer new solutions for secure data management. The concept of AI in personalized healthcare is also driving innovation in how data is secured and utilized.
Best Practices for Hospitals and Manufacturers
To ensure robust cyber-physical security for connected pacemakers, both hospitals and manufacturers should adopt the following:
For Hospitals:
- Asset Inventory: Maintain a comprehensive list of all connected medical devices.
- Risk Management: Regularly assess and prioritize security risks.
- Incident Response Plan: Develop and test a clear plan for handling security breaches.
- Vendor Security Management: Ensure third-party vendors adhere to strict security standards.
- Continuous Monitoring: Implement systems for ongoing security monitoring.
For Manufacturers:
- Security by Design: Integrate security from the initial design phase.
- Secure Development Lifecycle: Follow secure coding practices and testing protocols.
- Post-Market Surveillance: Monitor devices in the field for emerging threats.
- Transparency: Communicate openly about device security features and vulnerabilities.
- Collaboration: Work with healthcare providers and cybersecurity experts.
Ultimately, a proactive and collaborative approach is essential. This ensures that technological advancements in healthcare do not come at the expense of patient safety.
Frequently Asked Questions (FAQ)
What are the main cybersecurity risks for connected pacemakers?
The main risks include unauthorized access, alteration of device settings, data breaches, and denial-of-service attacks. These could lead to dangerous physiological effects.
How can hospitals protect connected pacemakers?
Hospitals can protect them through network segmentation, strong access controls, regular security audits, and robust intrusion detection systems. They must also ensure devices are properly inventoried and managed.
What is the responsibility of medical device manufacturers?
Manufacturers are responsible for designing devices with security in mind, implementing secure software and firmware, and providing timely updates. They must also conduct thorough risk assessments.
Are current pacemakers vulnerable to hacking?
While manufacturers are continuously improving security, some older models may have vulnerabilities. It is crucial for healthcare providers to stay informed about known risks and apply available patches.
What is the difference between cybersecurity and cyber-physical security?
Cybersecurity focuses on protecting digital information and systems. Cyber-physical security extends this to include the interaction between computational systems and the physical world, which is critical for medical devices.
Conclusion
The integration of connected devices like pacemakers represents a significant leap forward in healthcare. However, it also introduces complex cyber-physical security challenges. IT security experts and medical device engineers must work hand-in-hand. They need to build a secure ecosystem. This ecosystem protects patients and their sensitive data. By prioritizing security from design to deployment and beyond, we can harness the full potential of connected healthcare safely and effectively. Therefore, continuous vigilance and adaptation are key to safeguarding patient well-being in this evolving technological landscape.

